“Hello CTU, we have been seeing multiple clients being targeted by a similar attack.”
Early Monday, March 1, Secureworks Security Operations Center (SOC) analysts sent this note to Secureworks® Counter Threat Unit™ (CTU) researchers. The night prior, Secureworks® Taegis™ XDR (Extended Detection and Response) detected malicious activity via our endpoint telemetry across several customers as Microsoft Exchange servers attempted to run a version of China Chopper web shell, all following a similar pattern of behaviors around the same time overnight in the United States and Europe.
Initial Response and Findings
The SOC’s note initiated our routine response, engaging CTU researchers, Incident Response Teams, SOC analysts, and Taegis engineers to collect critical, relevant intelligence such as initial attack vector, attack failures and successes, impacted customers (by looking back over a year’s worth of event data), and importantly, understanding the intent. Secureworks Director of Intelligence Mike McLellan outlined our initial findings and hypotheses in the blog Government-Sponsored Campaign Targets Microsoft Exchange Vulnerabilities.
In this event, endpoint telemetry was critical to detecting and understanding the threat. By looking back across customers’ endpoint telemetry, we identified related intrusion activity across our customer base. Additionally, the CTU was able to add new threat indicators and Countermeasures to the existing detections that first triggered the initial alert.
Once we had a comprehensive understanding of the threat and credible recommendations to provide customers, we released CTU TIPS to inform customers of the targeted campaign and provide initial recommendations, and XDR notified all customers of the threat at log-in. Additionally, Microsoft released out-of-band patches for on-premises Microsoft Exchange Servers that organizations with vulnerable systems should apply as soon as possible.
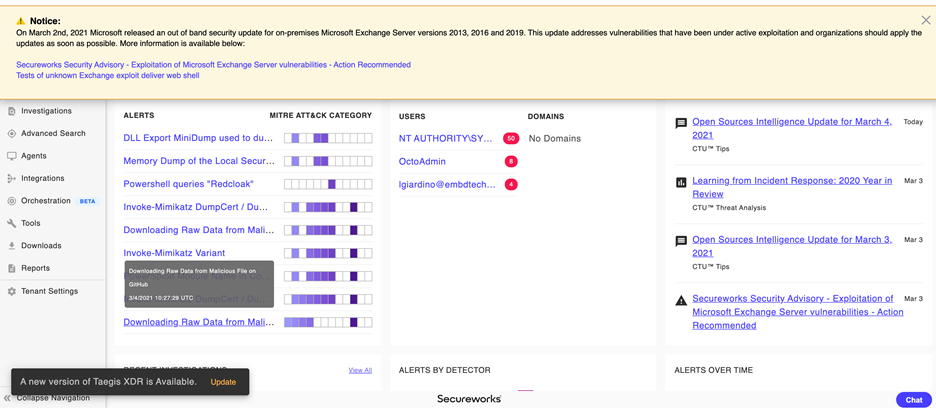
Figure 1: Secureworks Taegis XDR Security Analytics Platform Log-In Notice and Threat Intelligence Report Viewer
Leveraging Secureworks Taegis VDR
In addition to Taegis’ threat detection and response capabilities, our SaaS-based vulnerability management product Secureworks Taegis VDR (Vulnerability Detection and Response) helps customers to quickly identify and prioritize vulnerabilities in their environment. Secureworks automatically factor in specific vulnerabilities heightened by recent incidents and public interest into VDR and we’re currently building detections for CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 as details about this vulnerability continue to surface. We recommend that customers who use VDR search specifically for <software:“Microsoft Exchange”> using VDR’s built-in search query language to immediately accelerate their VM cycle outside of their regular scan and identify existing vulnerable assets (see Figure 2).
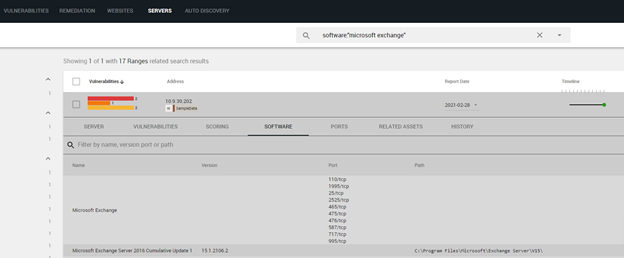
Figure 2: Secureworks Taegis VDR Search for <software:“Microsoft Exchange”>
The purpose of VDR’s contextual prioritization engine is to help customers more easily identify which vulnerabilities create the highest risk in their environment. That risk is always subject to each organization’s internal context, from which VDR continuously learns. In this case, as the attack is exploiting unpatched on-premises Exchange Server versions 2013, 2016, and 2019, VDR will help impacted customers understand which of the occurrences of the above CVEs to address first, saving security experts critical triaging time. Customers can either search specifically for Microsoft Exchange, as shown in Figure 2, or reliable detections for these CVEs, once those are available, to confirm that this incident is or is not a priority in comparison to other vulnerabilities within their environment.
Secureworks Incident Response (IR) Engagement Support
The IR team immediately started working with customers who had seen exploitation of their Microsoft Exchange servers from this activity, providing guidance on the remediation steps and identifying any further activity. As always, Secureworks Incident Response is at the ready, both for new customers who need emergency incident response or for customers with existing retainers.
Additional Steps You Can Take
We recommend that organizations take the following steps, if applicable, to keep their organizations safe:
- If you have on-premises versions of Exchange with the vulnerability, and you have concerns, invoke your incident response, whether it’s through our team, internally or through your Managed Security Services Provider (MSSP), to investigate whether access has been leveraged by the threat actor that Microsoft is currently referring to as HAFNIUM.
- Organizations using affected on-premises versions of Exchange Server should apply updates immediately, if possible. Please note that Exchange Online is not affected.
- Organizations should also closely monitor Exchange Server logs for relevant threat indicators, ensure a good EDR product to detect behaviors and apply indicators (e.g., Secureworks endpoint agent or one of our endpoint partners), and consider restricting access to the Microsoft Exchange Control Panel (ECP).
- If you are an existing VDR customer: Search for <software“Microsoft Exchange”> for a specific scan and continue to prioritize the highest risk in your environment.
Our Taegis security analytics platform, CTU researchers, IR team, and SOC analysts will continue to work together, leveraging the most relevant and current intelligence in service of our customers.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

