Many customers struggle with identifying and protecting their most critical digital assets. What assets are most vital to keeping your organization running and working toward its mission? And once they've figured that out, what are the cybersecurity defense strategies to protect them, detect attacks against them, and respond to those attacks?
There are often actions in security that seem easy on the surface but are much harder than they appear. One of those supposedly easy things is knowing what's most critical to your business. This is the first step to protection — asset management — because you quite simply can't defend what you don't know you have.
Step 1: Making a list
You should start by making a list of your important assets. Ideally, you'd import these into a continuously updated asset management system, but most companies don't have real-time asset management. Don’t let that stop you. When it comes to asset management, and specifically protecting those most vital assets, almost anything is better than nothing. What's most important is that it's thoughtfully put together and regularly prioritized and updated.
Step 2: Find your critical assets
Unfortunately, many organizations now run into a worse problem: not knowing where most of their most critical assets are. In that case I recommend two exercises that will pull those assets into the open.
These exercises take a data-centric approach to critical assets, which is a common approach that I prefer, but some go with a systems-based approach rather than data. It works much the same but focuses on key servers rather than key datastores.
- Make a map of your infrastructure. Start with your main offices or cloud providers. Add your datacenters. Add your employees, whether they're onsite, remote, or both. Add your vendors that you share data with (start with the main ones if there are too many to list).
- Make a list of your business processes. Open up your company's website and look at all the different products, services and offerings that are available there. Then using the diagram of your company's infrastructure combined with what you know your company offers, make a list of all the various business flows that must take place for the business to function. For example: Customer Sign-up, Customer Product Purchase, Paying Employees, Paying Vendors, Onboarding a New Vendor, Using Contractors, Transferring Money to Partners, etc.
- Map those business processes onto your architecture map. You'll have to add components as you go, which is a good thing. You'll start to see things like your domain provider, your network edge, your websites, your application servers and your databases. You'll often need to consult with many internal experts to fill in this picture, as there aren't many people in medium to large-sized companies who can see the whole thing in detail.
What emerges from this exercise is an incredibly rich picture of how the company works, and — most importantly for this topic — where data is moving and being stored. Those locations will continue to feature as you add more business processes, and it'll soon be clear which ones are primary.
Step 3: Prioritizing your assets
Now that you've identified some key systems such as servers, databases, vendors, or some combination thereof, you can now prioritize them. There are many methods for doing this, but one that I've used successfully in the past is labeling the data streams with the data classifications used at the company.
If you label those flows at the highest level of data used, you can then mark the datastore it's sent to as that level as well. If your data classifications are Confidential, Sensitive, Private and Public, each business process flow will have such a label, and each datastore will have one as well. You'd be surprised how many datastores quickly come to have the highest data classification, and how many people you interview during the process who had no idea that such data was stored there.
This will result in a set of datastores — probably far more than you anticipated — that are in need of protection. And be sure to note that a large portion of these may be SaaS providers, or in many cases the data is being sent to such a provider for filtering or replication. Those have to be protected as well. It may be that you decide not to manage that risk actively, since that vendor presumably passed a security check to be able to receive that data. But given the difficulty of vendor security management, you should keep these external datastores on your radar (asset sheet). Remember, if your customers' data gets leaked, you will still have to deal with the aftermath, even if it wasn't you that was hacked.
Each of these should now be an entry in your asset management system. But for the sake of realism, let's just call it a spreadsheet, because that's what it is for most people. Now, given what you know about the business, and from all the interviews you've had to construct the architecture diagram and all your business flows, you should be able to pretty easily prioritize the datastores. Some obvious methods include counting how many business processes store data there, how highly rated the data is, or the quantity of data stored there.
Step 4: Documenting the controls
Once you have them rated by priority (a simple ordinal list is fine), you can start at #1 and fill in the following attributes in additional columns:
- Number of key business processes storing data there
- Highest data classification of data stored there
- Platform (MySQL, Postgres, Aurora, etc)
- Environment (AWS, on-prem, etc)
- Encryption (YES, NO)
- Encryption Type (Database, Row, etc.)
- Backups (YES, NO)
- Backup Type
- Backup Location
- Backup Frequency
- Restore Tested?
- Last Successful Restore Test Date
- Audited?
- Last Audit Date
- Penetration tested?
- Last Pentest Date
This may seem like a lot of information, but these are just a few of the attributes you could use for this type of prioritization
These are attributes of the datastore's security, and the processes to support that security, that are essential to know about each entry in your spreadsheet. After filling this in, you will likely start to see major gaps. A narrative of this process might sound something like this:
"Oh, it looks like we're storing most of our data here. But it's full of unencrypted Confidential data, we've never had an audit or any pentesting against it, and we're not doing backups."
Discovering those misses is precisely the benefit of this approach. It shows your weaknesses in clear terms and allows you to spin up projects to fix the issues.
Ideally this would all be automated, which is possible with a number of platforms out there today, but don't let the ideal be the enemy of the essential. Go ahead and use a free application such as Notepad — don’t let systems stop you from exercising your audit muscles.
Doing this simple exercise, keeping it regularly updated (quarterly or semi-annually), and implementing projects to lock down what you find will be immeasurably valuable to your company. Only when you know what you want to protect and where that data is stored can you enact cybersecurity defense strategies and dive deeper into understanding what solutions you need to ensure threat actors don’t gain access to your critical information. Many find their data is stored across environments (endpoints, cloud, business applications) and those accessing data have varying levels of access rights. When this is the case, your best strategy to protect that content is to ensure you have full visiblity across your entire IT landscape so you can detect and respond to threats with fast, automated response actions before damage is done.
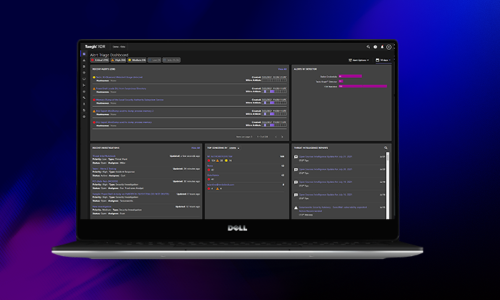
This is why cloud-native cybersecurity platforms for threat prevention, detection and response are so valuable in helping organizations secure their critical assets, regardless of where data is secured. You can see how Secureworks® Taegis™ works in this short attack video: A Deeper Look Into How XDR Powers Rapid Attack Detection and Response Video.
You Might Also Like
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.