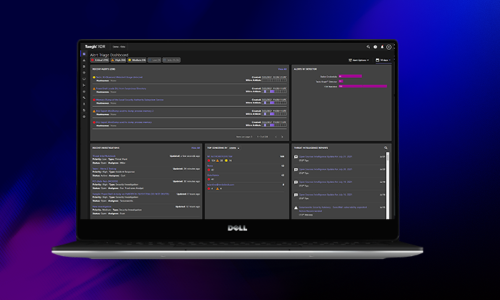
Watch a technical demonstration of how Taegis™ XDR enables quick detection and response to an attack.
In this technical video, you will watch:
- The specific steps a cybercriminal takes to attack a vulnerable Microsoft Exchange Server
- How a defender using Taegis™ XDR quickly detects and responds to multiple stages of the attack
Get a front seat view of common tools and techniques that attackers use to gain access to a vulnerable Microsoft Exchange Server, then escalate privileges and move laterally within the network to ultimately gain complete control.
Watch how Taegis XDR identifies and correlates related events at multiple stages of the attack. Through prioritized alerts and visibility into the attacker’s every move, see how security analysts are empowered to successfully detect and respond before the damage can be done.