- Author: Dell SecureWorks Counter Threat Unit™ Threat Intelligence
- Date: 21 March 2013
Overview
On March 20, 2013, at approximately 14:00 KST (UTC+9), three major broadcasting companies and six of the major financial institutions in South Korea (Republic of Korea) reported cyber security incidents. The attacks caused outage and delay in critical systems at banks and media outlets.
Dell SecureWorks analysts acquired malware samples for further analysis. This report focuses on the technical analysis of the destructive malware samples and CTU researchers' analysis on open source intelligence.
Affected organizations
| Financial Sector companies | Media companies |
| NongHyup | KBS |
| Shinhan Bank | MBC |
| Jeju Bank | YTN |
| NongHyup Insurance (Subsidiary of NongHyup Financial group) | |
| LotteCard (Shinhan Bank related) | |
| Woori Bank |
Table 1. List of affected organizations (Source: SEWORKS)
Dell SecureWorks located a Korean article that one of the major ISP data centers (LG Uplus) may have been compromised, but no technical evidence was provided at publication time.
The South Korean government announced that more than 30,000 hosts (server and personal computers) are affected by this incident.
Technical analysis of the Wiper malware
Dell SecureWorks acquired three malware samples that match the characteristics and behaviors associated with these attacks (see Figure 1).
| MD5 | File Size | Identification |
| 9263e40d9823aecf9388b64de34eae54 | 427,520 bytes | Dropper |
| db4bbdc36a78a8807ad9b15a562515c4 | 24,576 bytes | Wiper A |
| 5fcd6e1dace6b0599429d913850f0364 | 24,576 bytes | Wiper B |
| 0a8032cd6b4a710b1771a080fa09fb87 | 24,576 bytes | Wiper C |
Table 1. Wiper malware characteristics. (Source: Dell SecureWorks)
Dropper
The dropper contains an icon in its resource section that identifies the program as AutoServerCrasher, Version 1.0.
Figure 1. AutoServerCrasher 1.0 dropper. (Source: Dell SecureWorks)
Analyzing the file header of the dropper reveals a PE timestamp of March 20, 2013 04:07:02 UTC. The PE timestamp indicates when the executable file was compiled and linked. While the PE timestamp value can be forged, this specific value corresponds to 13:07:02 Korea Standard Time (KST). Public reports indicate that affected systems were crashing at approximately 14:00 KST.
The dropper extracts four files from its resource section and saves them to the victim's Temp directory.
| MD5 | File Name |
| db4bbdc36a78a8807ad9b15a562515c4 | AgentBase.exe |
| e45cd9052dd3dd502685dfd9aa2575ca | alg.exe |
| 6a702342e8d9911bde134129542a045b | conime.exe |
| dc789dee20087c5e1552804492b042cd | ~pr1.tmp |
Table 3. Extracted file characteristics. (Source: Dell SecureWorks)
The dropped file AgentBase.exe is a match for the Wiper samples obtained by the CTU research team. The additional files are:
- alg.exe - UPX compressed version of Simon Tatham's PuTTY SSH client.
- conime.exe - UPX compressed version of Simon Tatham's PuTTY SCP client.
- ~pr1.tmp - A Bash script designed to overwrite and/or delete key system directories and partitions on various Unix-based operating systems.
The dropper checks for the existence of the file C:\windows\Temp\~v3.log. If the file is not present, the dropper runs the AgentBase.exe wiper program.
The 'v3.log' file is a log file created after Ahnlab's (one of the most popular antivirus vendors in South Korea) antivirus product is successfully installed on the host. Dell SecureWorks believes the dropper is using this file as an indicator of whether AhnLab's antivirus product is installed on the system. Later sections in this analysis describe this malware's behavior depending on the detection of the log file.
The dropper scans through all the user directories it has access to on the system, looking for specific files that indicate that the mRemote or SecureCRT remote management tools are installed. If these tools are found, the dropper searches for the application files that contain stored session information. The dropper will specifically look for stored sessions data that use the SSH protocol and contain the root user and stored password. The dropper parses out the remote server and root password information and uses conime.exe to copy ~pr1.tmp to these servers.
<conime.exe path> -batch -P <port> -l root -pw <password> <~pr1.tmp path> <server>:/tmp/cups
The dropper uses alg.exe to run the Unix wiper on the remote host:
<alg.exe path> -batch -P <port> -l root -pw <password> <server> "chmod 755 /tmp/cups;/tmp/cups"
Despite scraping SSH credentials to install and run the Unix wiper script, the dropper does not attempt to store the credentials to disk or transmit the credentials to a remote command and control (C2) server. The dropper does not contain any network communication or remote access functionality.
Unix Wiper
The ~pr1.tmp Unix wiper tool is a basic Bash script that determines the system type by running the uname -s command. It checks for the following values:
- Linux
- AIX
- SunOS
- HP-UX
If one of these values is found, the script calls the appropriate function for that operating system. ~pr1.tmp uses the dd command (which converts and copies a file) to overwrite certain partitions with all zeros and the rm command to remove critical system directories.
Windows Wipers
In addition to "Wiper A", the malware linked to the dropper file obtained by the CTU research team, two additional and related wiper tools were found. These wiper tools are likely associated with additional droppers that have yet to be discovered.
Common behavior
The core functionality of all three Wiper programs is to overwrite sections of the infected computer's hard drive, including the Master Boot Record (MBR), in an attempt to render the computer unable to function and a potential loss of all stored data.
All three samples perform several operations typically found in shellcode or other Position Independent Code (PIC) programming. Wiper obtains the Extended Instruction Pointer (EIP) value using a call/pop trick. It also attempts to resolve several API functions by performing a checksum operation on the function names exported by a specific library and comparing them with values stored in the malware. This behavior indicates that the author of the Wiper tools either has knowledge of assembly language programming or access to toolkits that could produce code in this format. Also, it appears that the Wiper code was "spliced" into an already existing executable file.
All three Wiper programs use the WinExec function to run the following commands:
taskkill /f /IM pasvc.exe
taskkill /f /IM clisvc.exe
Pasvc.exe is a filename associated with AhnLab antivirus software. Clisvc.exe is associated with Hauri antivirus software.
All three samples also attempt to reboot the computer by issuing the command:
shutdown -r -t 0
These arguments indicate that the infected system should reboot immediately.
The Wiper samples do not contain any additional information theft and backdoor functionality.
Master Boot Record / Volume Boot Record corruption
All three Wiper samples attempt to overwrite the MBR and VBR by iterating over the first 10 physical disks (e.g. \\.\PhysicalDrive0) and overwriting the MBR and VBR areas with repeating instances of a specific string. This string varies across different Wiper samples.
Logical drive corruption
On Windows 2000, Windows XP, and Windows Server 2003, all three Wiper samples look for logical drives mounted as drive letters B through Z. Wiper checks if the drives are of type DRIVE_FIXED or DRIVE_REMOVABLE. If they are, Wiper overwrites these drives with a repeating string pattern. Therefore, any attached removable drives, such as a USB thumb drives, would be at risk of being wiped. Wiper attempts to overwrite the logical drives by writing to the physical file path for the drive (e.g. \\.\c:)
On Windows Vista and later Windows operating environments, the Wiper scripts attempt to overwrite each file with a specific string pattern. They then attempt to remove any directories. The following directories will not have their files overwritten and any subdirectories and files contained within will not be removed:
- c:\windows
- c:\Program Files
- c:\ProgramData
Wiper A
This sample searches for a file with the path %SYSTEMROOT%\Temp\~v3.log. If the file exists, the malware will exit.
Wiper A uses repeating instances of the string 'PRINCPES' to overwrite the MBR and Volume Boot Record (VBR) and the string 'PRINCIPES' to overwrite logical drives.[1]
Wiper A does not check for a specific time before running.
Wiper B
Wiper B does not check for the existence of the %SYSTEMROOT%\Temp\~v3.log file.
Wiper B uses repeating instances of 'HASTATI.' to overwrite the MBR, VBR, and logical drives.
Wiper B checks the local time. If it is earlier than March 20, 2013 14:00, then Wiper B will sleep and periodically check the local time. Once it is equal to or later than March 20, 2013 1400, Wiper B will continue executing.
Wiper C
Wiper C creates a string for the path c:\windows\Temp\~v3.log, but it never checks if the file exists.
Wiper C uses repeating instances of the string 'PR!NCPES' (note the exclamation point in substitution of the "I" character) to overwrite the MBR, VBR, and logical drives.
Wiper C does not check for a specific time before running.
Additional threat indicators
Registry
None of the Wiper samples analyzed by the CTU research team make any changes to the Windows registry.
Network
The dropper file attempts to connect to other servers via SSH to copy and execute the Unix wiper script. However, these connections would be to servers that are normally accessed from the infected computer.
None of the Windows-based Wiper samples initiate or accept network connections.
Named objects
All three Windows-based Wiper scripts create a file mapping object with the name JO840112-CRAS8468-11150923-PCI8273V. Instead of mapping a specific file on disk to memory, the Wipers create a special mapping object against the system page file. This is a common technique used for shared memory between processes. However, the purpose of Wiper creating this file mapping object is unclear, as the malware never uses the object after it is created.
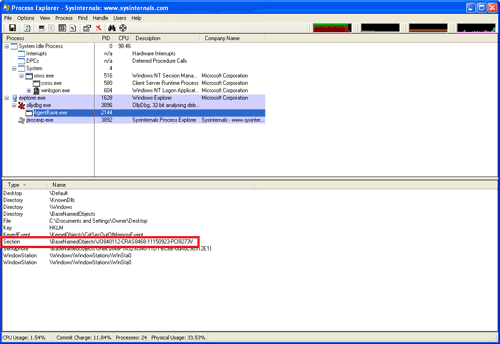
Figure 2. Wiper named object creation. (Source: Dell SecureWorks)
Given the destructive nature of this malware, this indicator will be short-lived.
Open source analysis
Malware distribution
The malicious code samples that Dell SecureWorks analyzed do not possess a self-propagating feature. The malicious code, that is, the dropper, must have used a separate method to be delivered to the targeted victim's host. Dell SecureWorks located a Korean government's press release reporting that the antivirus software Patch Management Server (PMS) was used to push the malicious file to victim hosts.
Data center compromise
A number of public sources raised the possibility of an ISP or data center compromise that lead to the incident. Dell SecureWorks is not certain of the location of the compromised PMS, or whether the PMS was located in a corporate network or collocated in a data center. The fact that multiple organizations were affected by the same malware in the same fashion of distribution strongly supports the possibility that PMS systems may have been hosted in the ISP's data center and were granted or acquired unauthorized access. However, there is no technical evidence that supports this scenario. There are many ways an attacker could infect customers with malware. The infection vector may not be related to Internet services, but instead to desktop maintenance or server administration. Dell SecureWorks is aware that Korean antivirus vendors and Korean analysts are also investigating data center logs to discover and confirm any relationships between the ISPs and the malware.
Actor
Dell SecureWorks has discovered several reported scenarios from public intelligence sources, all supported with partial facts.
Dell SecureWorks does not have technical evidence supporting any of the reported scenarios at publication time.
Whois group
Dell SecureWorks located an article regarding a group called 'WHOIS" claiming responsibility for this incident. However, the reliability of this information has been challenged due to the group's poorly maintained webpage and lack of past history of the group.
China
The South Korean government announced that a Chinese IP address has been found in the access log of the compromised PMS system. This fact only indicates the last hop of the abnormal access to the PMS was identified to be assigned in China. Further log analysis of the compromised PMS system may clarify the Chinese IP address involvement in this incident.
North Korea
Dell SecureWorks is aware of the IP address in China associated with this attack and the speculation relating to the attacks originating in either North Korea or China being state sponsored. While these speculations are possibilities, there is insufficient evidence at this stage of the investigation to make any such statement with certainty. There are no direct Internet connections from North Korea to South Korea and it is plausible that any attack to South Korea could follow a path that leads through Chinese IP space regardless of who the attacker(s) may be. Because of this fact pattern we cannot, at this time, state with a degree of certainty the origin of the attacks.
Islamic or Middle East
This possible scenario is raised because the 'Wiper' malware was used recently in the Shamoon and Iranian attacks. The skull logo used by the 'WHOIS' hacking group's webpage is commonly used by Middle Eastern or North African groups.
Indicators
Dell SecureWorks conducted research using the Threat Intelligence Management System (TIMS) at the heart of the Dell SecureWorks Targeted Threat Surveillance service to finding relationships with known malicious activity or other characteristics. CTU analysts used the 101.106.25.105 Chinese IP address mentioned in Korean government's announcement.
According to TIMS, this specific IP address does not have a history of involvement in APT attacks or C2 resources. When Dell SecureWorks expanded the search to the entire network band (four B-Class IP address ranges) owned by the Chinese organization, the trending graph identifies numerous executable file download activity over HTTP.
Given that the executable file download attempt over HTTP is a generic event, it is difficult to determine if the activity is connected to the incident. However, CTU analysts find this trend interesting, as the timeline graph in Figure 3 indicates that this activity was elevated in February, 2013, one month before this incident.
Dell SecureWorks continues to conduct relational threat indicator analysis using TIMS as new indicators are discovered.
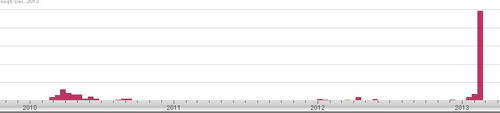
Figure 3. Timeline of executable file download events over HTTP. (Source: Dell SecureWorks)
Timeline
Source: DongA newspaper http://news.donga.com/Main/3/all/20130320/53842793/1
| Time Stamp (KST, UTC+9) | Description |
| 14:15, 03/20/2013 | Major media corporations and banks in South Korea identified unusual activity on internal systems. |
| 14:22, 03/20/2013 | KCC (Korea Communications Commission) and KISA (Korea Internet Security Agency) received incident report. |
| 14:29, 03/20/2013 | KCC, KISA, NCSC (National Cyber Security Center) and Police CTRC (Cyber Terror Response Center) initiated coordination efforts. |
| 14:37, 03/20/2013 | Initiated investigation by supporting on-site analysis. |
| 14:50, 03/20/2013 | South Korean President Park ordered recovery in a timely manner and also ordered a thorough investigation to find the root cause of the incident. |
| 15:00, 03/20/2013 | South Korean government raised the Internet Security Response level from 'Attention' to 'Alert'. |
| 15:05, 03/20/2013 | South Korean ISPs, antivirus vendors and mobile service providers were asked to report any abnormal activity detected. |
| 15:30, 03/20/2013 | ISPs confirmed no abnormal traffic patterns were detected. |
| 15:50, 03/20/2013 | One of the LG groupware clients confirmed compromise. |
| 16:15, 03/20/2013 | KCC announced a possibility of malware activity related to the incident. |
| 16:21, 03/20/2013 | One of the antivirus vendors acquired a malware sample. |
| 17:00, 03/20/2013 | KISA confirmed that the incident is limited to domestic, not global impact. |
Table 4. Timeline of activity for this malware.
Lessons learned
- This incident demonstrates the importance on securing and managing security controls (for example, PMS, IDS, firewalls, etc.) in the organization, as opposed to adopting new technology or purchasing additional security products. Vulnerable security control resources can be misused for compromising internal resources, because the security control systems are listed as a trusted host(s) in the environment.
- Not only security administrators need to secure the security control resources. Vulnerable security products can be used as a target to distribute malicious code. The requirement for secure coding efforts and methodologies is highlighted, especially for security products.
- Because the dropper enumerates the victim's directory for SSH session information containing root users and saved passwords, customers should control how privileged users access remote servers (i.e. prohibiting remote SSH as root) and minimize external access to the trusted system in the organization.
Remediation and detection
The Wiper malware is not directly transmitted over the Internet (it is dropped by another program), making it difficult to detect using a network-based countermeasure. Additionally, the dropper program is UPX-packed, which makes it difficult to reliably identify content anchors unique to this malware.
Many antivirus companies have detection for this malware under a variety of names, including Jokra, KillMBR, Dembr and several others. At publication time, the VirusTotal service identifies the following detection rate for these malware samples:
- Dropper - 28/45
- Wiper A - 34/43
- Wiper B - 32/45
- Wiper C - 33/45
Customers can search for specific file indicators as identified in this threat analysis and ensure the integrity of patch management systems by limiting access outside the corporate network.
Dell SecureWorks is aware that South Korean government agencies and antivirus vendors provide a malicious code removal tool for free. However, this tool is only affective before the MBR compromise happens. Once the Wiper code is executed and the MBR is compromised, followed by a system shutdown, victims cannot boot the system to run the removal tool.
There is a suggested mitigation technique to change an infected system's CMOS system clock to a value prior to the March 20, 2013 date. CTU researchers have discovered that some Wiper variants become active independent of the system time.
Dell SecureWorks recommends that customers monitor for unauthorized access to critical systems and ensure that systems are up to date.
Conclusion
The analysis and conclusions regarding this incident and its effects are still ongoing. The Dell SecureWorks CTU research team continues to analyze additional related malware and coordinate with international partners.
References
ASEC Blog, "Major broadcasters and Bank network failure caused by malware" (translated from Korean) http://www.microsofttranslator.com/bv.aspx?from=&to=en&a=http://asec.ahnlab.com/926. Original article at http://asec.ahnlab.com/926
dongA.com newspaper, "Broadcasters attack situation highly hack"(translated from Korean) http://www.microsofttranslator.com/bv.aspx?from=&to=en&a=http://news.donga.com/Main/3/all/20130320/53842793/1. Original article at http://news.donga.com/Main/3/all/20130320/53842793/1
SEWORKS, "Major public media and Bank sites Cyber Terror Analysis Report" (report is in Korean), http://www.seworks.co.kr/report20130320.pdf
Sophos blog, "DarkSeoul: SophosLabs identifies malware used in South Korean internet attack," http://nakedsecurity.sophos.com/2013/03/20/south-korea-cyber-attack/
Stratigos Security blog, "South Korean Media and Banks under Cyberattack", March 20, 2013, http://stratigossecurity.com/2013/03/20/south-korean-media-and-banks-under-cyberattack/
Yonhap News Agency, "Malicious code in NongHyup system came from Chinese IP: gov't" http://english.yonhapnews.co.kr/techscience/2013/03/21/81/0601000000AEN20130321003751320F.HTML Original article at http://media.daum.net/issue/460/newsview?issueId=460&newsid=20130321110011027
![]() [1]http://en.wikipedia.org/wiki/Hastati
[1]http://en.wikipedia.org/wiki/Hastati
Although Dell SecureWorks is not certain whether the author of the malicious code followed the ancient Roman tactics, known as the polybian system, the strings used for overwriting the MBR area follows the ancient battle line strategy - Hastati, Principes and Triarii. Dell SecureWorks has analyzed two Wiper samples that use 'HASTATI' and 'PR!NCIPES' or 'PRINCIPES', but no sample has been discovered referencing 'Triarii'. This omission may possibly indicate an additional phase of the attack matching the ancient battle strategy.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.
