My manufacturing target was armed to the teeth. The challenge was waiting for me: a client with several well-known cybersecurity applications in place and a corporate password policy of 14-characters in length. From endpoint security and firewall, to identity and access management, this customer had all the gear!
“This is going to be a tough Internal penetration test,” I thought to myself. Battle ready in my favorite pajamas, I rolled up my sleeves to tackle the 15,000-user organization.
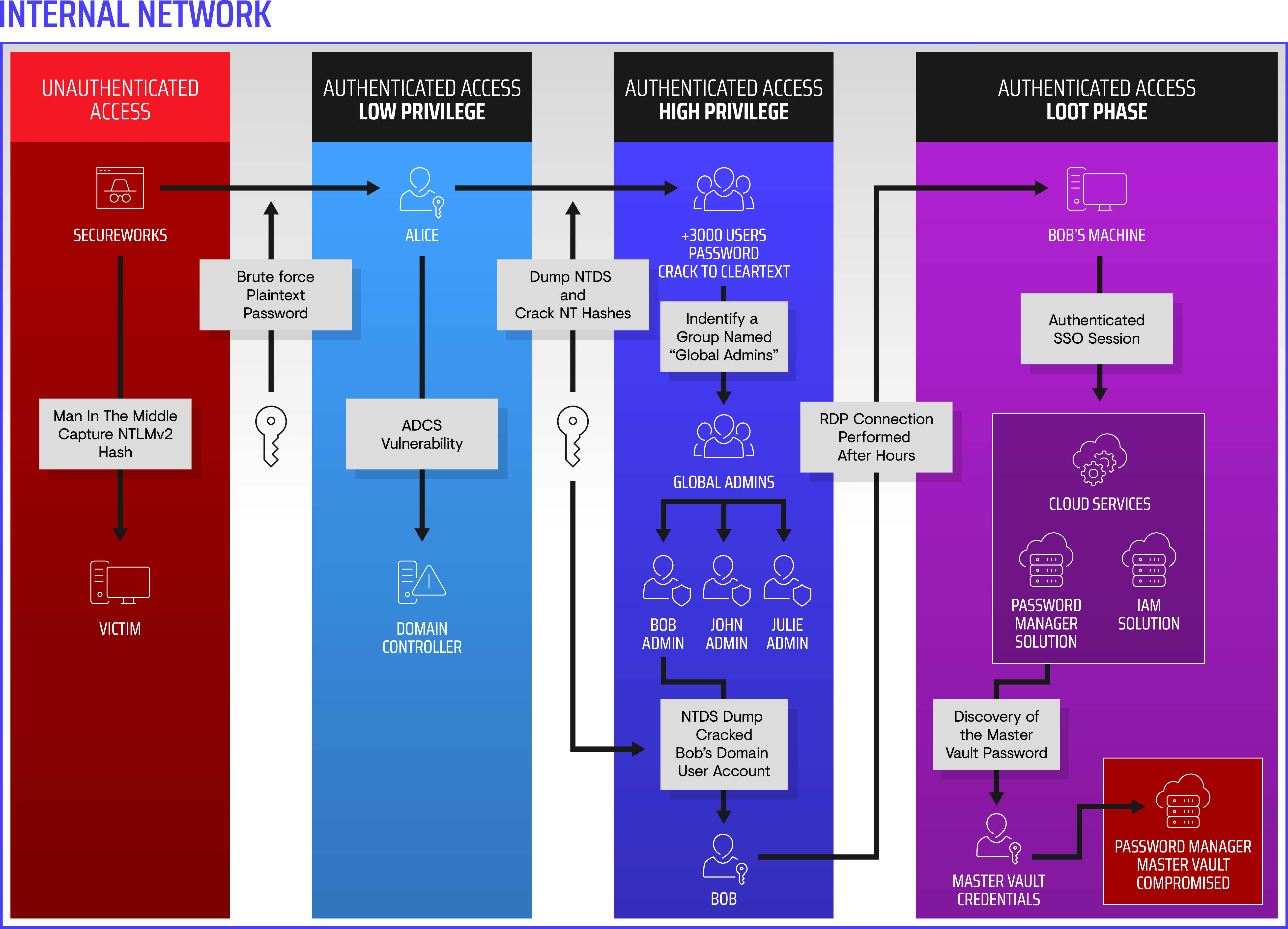
I tried the ol' Man-In-The-Middle Attack, some heavy-duty password cracking, ADCS Priv Esc, and a few other favorites. And by the second day in the field, just in time for my afternoon tea (I'm in the UK), Enterprise Admin access was gained. This meant that any systems within the organization's domain now belonged to me.
But this was just the first hurdle. Nowadays with cloud-services, gaining elevated-privileges in the internal domain is not enough — especially when these cloud services are protected by MFA.
The Domain Controller NTDS file containing all the passwords was dumped and sent to our proprietary password cracking rig. Despite a company-wide 14-character length password policy, around 3,500 passwords cracked to cleartext.
Next, I unleashed my companion, “Bloodhound,” and went on a hunting spree. Bloodhound is an open-source tool, able to ingest highly complex data from Active Directory and reveal unintended attack paths. Within just a few clicks, the results were revealed:
- 16,342 accounts
- 14,078 computers
- 1,037,046 relationships
Browsing through the results, a high net-worth group named "Global Admins" was identified containing seven Domain Admin accounts. No cleartext passwords for any of the Domain Admin accounts were recovered (the customer's existing identity security vendor was rotating them daily). But a Domain User account belonging to a Domain Admin had cracked.
In the middle of the night, I crept to my workstation and initiated an RDP connection to the Domain User's workstation. The employee was asleep but their session was still active, and the user was logged-in on various web portals. It was time to get more acquainted with this user's access! Flipping through the various tabs on the browser revealed admin access to various services, such as the Service Desk management portal. I opened a new tab and browsed to the management dashboard of their identity and access management software. The SSO session was still valid and no MFA was requested, leaving the vault open.
Here's where the adrenaline started pumping. The vast majority of accounts were for administrative purposes, but one entry caught my attention: the Admin credentials for the client's access management software. Within a new tab, a quick copy and paste of the username and password opened up the master vault containing all 3,968 passwords within the application's vault.
With this access, administrative privileges were gained to — how do I put this? — everything. I had access to every last piece of the puzzle, from the customer's endpoint security and domain management to their email service, all the connected services bundled in with it, and even their backup servers.
I took the liberty to screenshot the three alerts generated by their endpoint security vendor during the engagement when performing a credentials dumping attack. The internal penetration test (pentest) should have created more alerts, but tracking activity from the attacker's agent-less system is still a bit of a grey area for security solutions.
Remediation:
What could the organization have done to better protect their crown jewels? Let's specifically focus on the password manager vendor. The issues discovered were not due to the product itself, but rather due to a weak implementation. There should have been more compartmentation within the Password Manager. Using the principle of least privilege, the Domain User account should only be able to see credentials used by their role. The Master Vault should have requested a Multi Factor Authentication and only be granted to a handful of high-privilege IT administrators. Finally, a strict session time-out should have been implemented to avoid an idle session being stolen by a threat actor.
Conclusion:
Cybersecurity is often referred to as a chain. Threat actors only need to find the weakest link to break the chain and steal everything. We need nothing more to validate this fact than the spate of horrifying headlines about breaches that just keep coming. From password manager vendors who've experienced major damage from recent attacks to aspects of our infrastructure that are becoming more difficult to protect, our vulnerabilities are myriad, and they are universal.
This engagement was no different than the failures we see profiled in headlines — because they followed a similar objective. For example, in our customer's case, complete access was as simple as gaining access to the Password Manager Master Vault. Once access is gained, a threat actor can quickly have free reign against an entire company.
So that takes me to the real bottom line. This is where pentesting shows its value. Yes, security solutions are important. But they need to be configured adequately and more importantly, tested against a simulated adversary on a regular basis. Combining the two is the only way to prevent intrusions and ensure detection capabilities are efficient.
To learn more about how Secureworks® and its Counter Threat Unit™ can help you get ahead of the threat, visit www.secureworks.com/services/penetration-testing.
Infographic
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.