Dell SecureWorks' Counter Threat Unit™ (CTU™) has discovered that the hackers behind the Gameover ZeuS banking Trojan (the largest botnet targeting financial institutions) is in the midst of launching several malicious spam campaigns using the Cutwail botnet (the largest spam botnet currently on the underground market ) to lure new computer victims in order to steal their banking credentials and credit card numbers.
Forgoing any holiday related scams, the ZeuS gang is sending out millions of bogus messages made to look like they are coming from many of the top US banks and read: “You have received a new encrypted message or a secure message from [XYZ] Bank”. The message states that the bank is concerned about your privacy and has come up with a system so their customers can securely exchange emails containing personal information. They ask the recipient to download the attachment and register if you are a first time user.
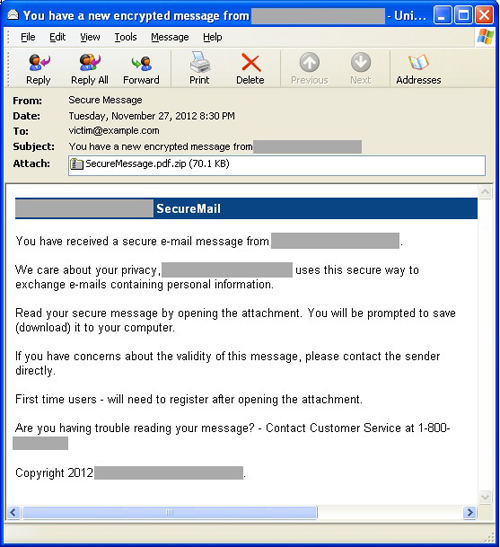
In actuality, when the attachment is clicked on, the user is executing the Pony downloader, which in turn installs the infamous Gameover ZeuS banking Trojan.
Previous work I did has shown that the Cutwail botnet only needs to employ approximately 10,000 bots per spam campaign to send out hundreds of millions of malicious spam messages to computer users all over the world.
The Gameover hackers are using several variants of this lure which include fake messages saying “you have received a fax or a scan or a voicemail and to open this message, you can download this program for free.” The CTU advises organizations to educate their employees about the current spam campaigns and remind them to never click on a link or an attachment in an email, even if they know the sender, and always verify that the sender sent the email. Additionally, update your IPS/IDS countermeasures and firewalls to detect.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

