This week a huge flaw in one of the key underpinnings of electronic commerce was discovered. For the last two years the Debian GNU/Linux version of OpenSSL has produced extremely weak keys. This was a classic case of the right hand not knowing what the left hand was doing.
A bit of background in cryptography is necessary to understand the problem. In order to create public-key cryptographic keys, a strong source of entropy is needed. OpenSSL uses uninitialized data (random bits in memory) as part of its pseudo-random number generator (PRNG). When Debian audited the OpenSSL code for memory management bugs the use of uninitialized data was flagged as a potential defect. The Debian package maintainers simply commented out the line of code causing the warning and moved along without realizing the full implications of their actions.
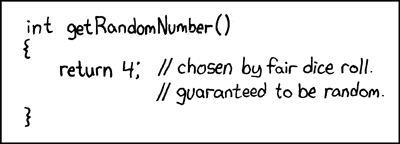
Unfortunately for users of Debian, without this uninitialized data the only entropy used by the OpenSSL PRNG is the process ID, essentially crippling it. This change limited the entire key space to 32,767 (2^15), instead of 2^1024 in the case of a 1024-bit DSA key.
Whoops.
Hackers have already generated all possible valid keys for x86 and have automated the task of brute forcing SSH. According to HD Moore "It should be possible to try all 32,767 keys of both DSA-1024 and RSA-2048 within a couple hours?"
There are two main points to bring away from this:
- If you are running a Debian box it's time to update your OpenSSL package and create new keys. Do it now. Do not pass go.
- You shouldn't take reports from auditing tools at face value. These are tools to point you in the direction of problems but they are prone to false positives. You should look into the 'problems' pointed out by these tools but they don't always necessitate major changes. In Debian's case the appropriate action would have been to add a comment explaining the purpose of that line of code rather than deleting it. This would have both made the code more readable and saved me a couple of hours earlier this week.
Picture courtesy of xkcd.com
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

