The Secureworks® Incident Response team has recently been very busy helping customers recover after post-intrusion ransomware attacks. In most cases, we see threat actors indiscriminately encrypt all assets they can deploy their ransomware to. Core IT assets like Domain Controllers, software deployment, and backup servers are knocked offline by the encryption process. By the time the dust settles, victims realize that many of the systems they rely on to investigate the breach, rebuild systems, and recover data are unavailable.
The worst-case scenario is having all of your Domain Controllers encrypted. That cripples authentication and name resolution for all Active Directory (AD) integrated services, making the simplest IT administration tasks challenging.
How do you deploy software if your software deployment mechanism can’t authenticate to AD? Does your backup solution still work? Can you recover data from your backups? The flip side of the convenience of Single Sign On reveals itself – once AD is down, it takes a lot of critical services with it.
Using Threat Actor techniques to enable emergency ransomware incident response
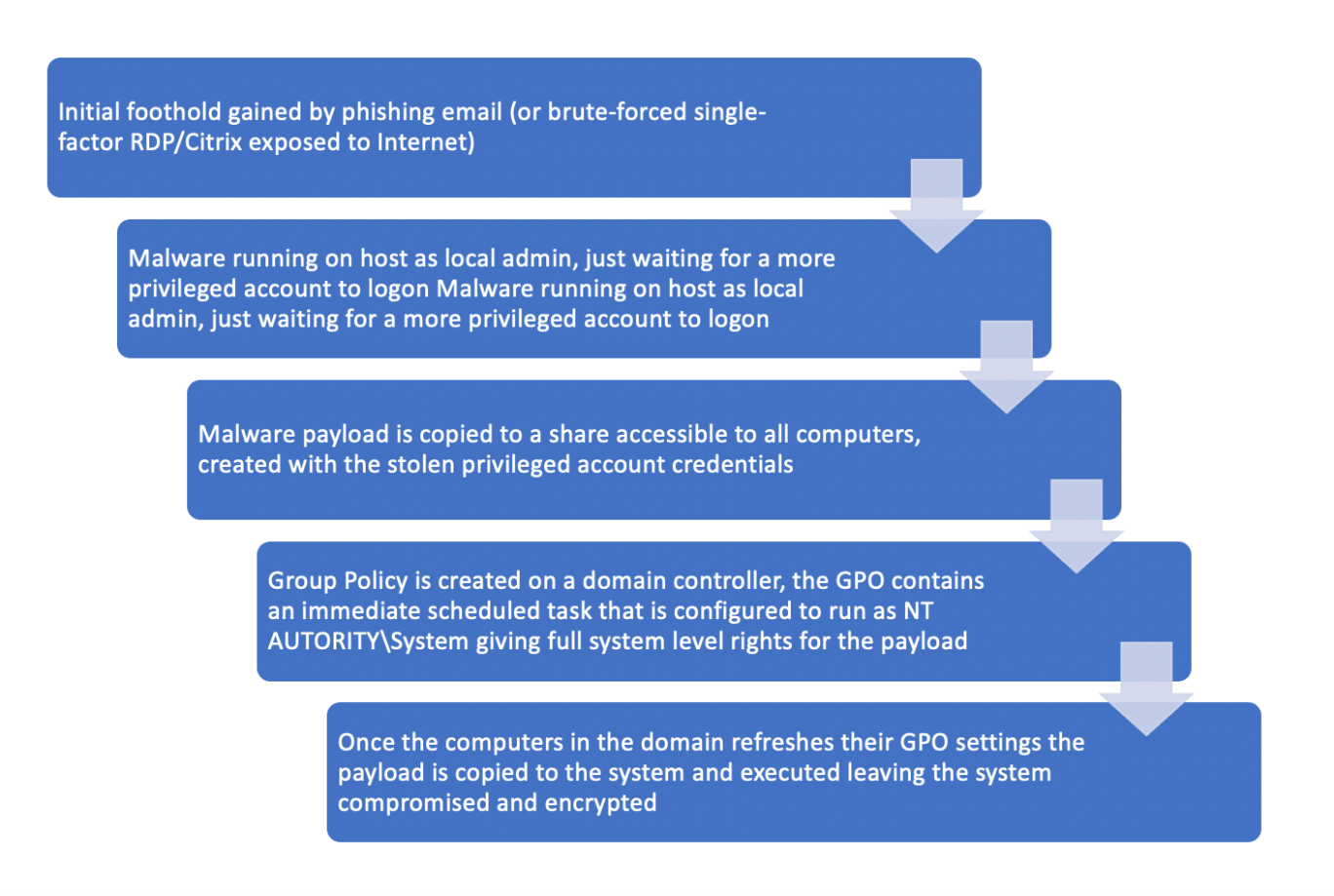
Often the threat actors will use AD to distribute their ransomware, just as we would use it for managing the domain on a daily basis. We see them using Group Policy Objects (GPOs) or PowerShell to install an immediate scheduled task on a wide array of systems.
The immediate scheduled task has some useful properties for the threat actor. It can run under various levels of privilege, and once executed it deletes itself from the system, leaving few traces.
Using GPOs, the threat actor can run their payload as NT AUTHORITY\System giving the malware full privileges over the system to install and disable whatever they want to.
Here is a summary of the usual steps in post-intrusion ransomware attacks:
Real-world example: Ransomware Incident Response
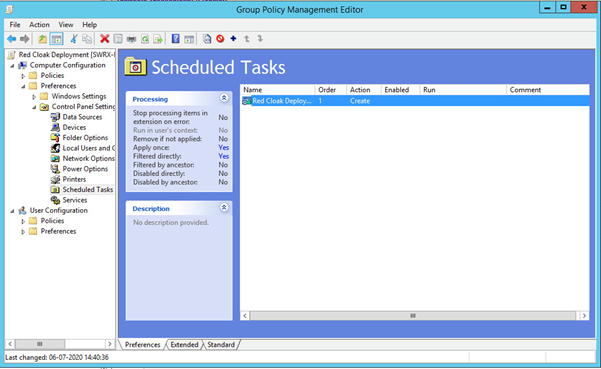
During a recent engagement, the threat actor successfully staged their attack using the active directory GPOs and an immediate scheduled task. The deployment of the payload encrypted a wide range of systems very quickly, including the software deployment system as well as many other line of business applications.
Normally we begin an IR engagement by deploying our Red Cloak™ Endpoint Detection and Response tool to gain as much visibility into the network as possible, to be able to help triage it and isolate any hosts that are needed to contain the compromise.
We needed to get the agent installed and, in this case, the customer was not able to do that because their software deployment tools were encrypted and non-operational.
So, what do you do when you need to deploy software and no deployment tool is operational?
We used the exact same method as the threat actor; we made a share and made sure that their only access to it was read and execute for domain computers. Why? We don’t want the chance of a persistent threat actor copying another package to the share with the same name – resulting in us distributing their payload.
Once the share was created, we copied the Red Cloak Microsoft Installer (MSI) to the share and tested the installer manually with the needed switches. After successfully testing the MSI, we created the GPO and linked at the top of the domain with the enforce option to ensure no block inheritance would stop the deployment.
Within the first 2 hours we had deployed to +2000 endpoints, and within 24 hours, +10,000.
For most Windows administrators, this is a simple task, but when your hair is on fire and nobody in the business can work because of a breach, it might be helpful to have a resource to guide you. If find yourself in that situation, you can reference the guide below.
Network Defender’s guide to deploying software in a hurry
What would this look like in practice? In the video below, we highlight the key steps IT admins would take to deploy an MSI if the regular software deployment mechanism was unavailable.

To learn more about why ransomware must be on every security professional’s radar, watch this presentation from our Director of Intelligence, Counter Threat Unit™ on Changing the Rules of Ransomware.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

