During a 2018 incident response engagement, Secureworks® analysts discovered strong evidence of a Russia-based espionage group using 'man-on-the-side' techniques to install malware on targeted networks. The threat actors used the same techniques in other incidents as well. This type of attack can undermine the integrity of the Internet's fundamental communications infrastructure.
What is a man-on-the-side attack?
A 'man-on-the-side' attack involves a threat actor subverting existing communications infrastructure to inject malicious content into legitimate traffic. To conduct this type of attack, the threat actor must first gain access to a network communications channel. They then leverage this access to monitor and manipulate network communications, including inserting malware into response traffic.
What was the initial discovery?
During this particular engagement, the Secureworks Advanced Endpoint Threat Detection (AETD) - Red Cloak™ solution detected that a system was compromised with the Karagany malware. This version [i] of Karagany is exclusively used by the Russia-based IRON LIBERTY threat group (also known as Energetic Bear and Dragonfly), which has historically targeted global energy, nuclear, and defense organizations. There were no obvious indications of where the malware came from — no evidence of a phishing email, no sign of a malicious download link, and no suggestion of a drive-by download.
What is the evidence?
A forensic analysis revealed a legitimate request to download an Adobe Flash installer around the same time that Karagany was downloaded. Figure 1 shows timeline data extracted from the master file table (MFT) from the compromised system's NTFS partition.
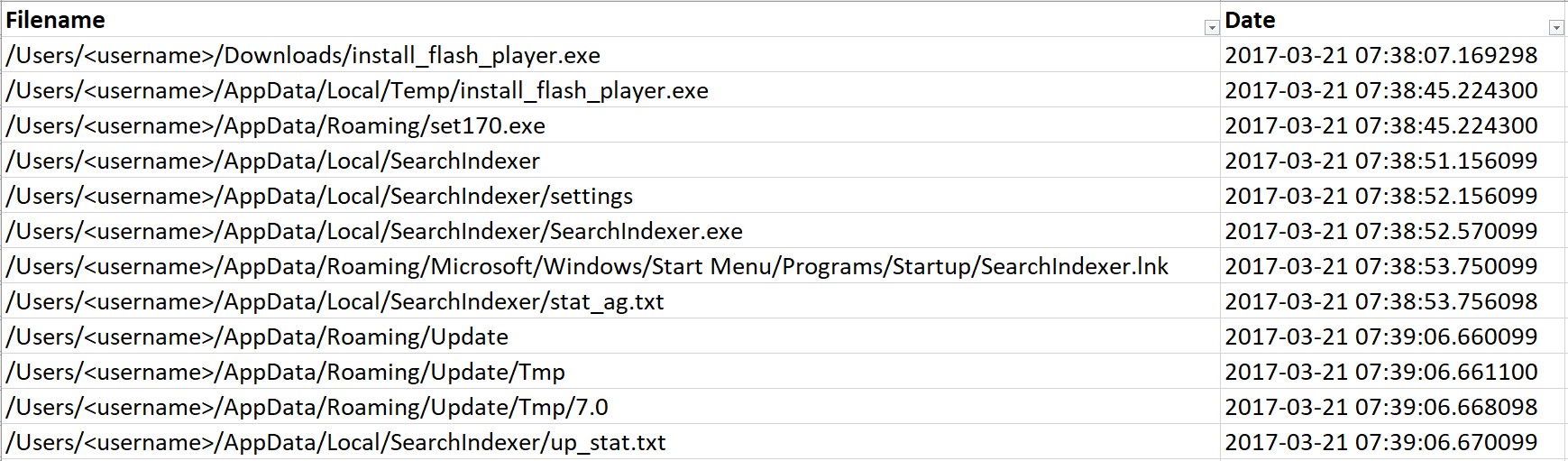
Figure 1. NTFS MFT showing the 'FN Info Creation date' of the Adobe and Karagany files. (Source: Secureworks)
In this instance, Karagany was installed on March 21, 2017:
- 07:38:07-07:38:25 — Chrome download logs indicate that an install_flash_player.exe file is downloaded to the user's Downloads directory after the user initiated a download over HTTP from adobe.com. This file was not present on the system at the time of the investigation and was not recovered.
- 07:38:45 — An install_flash_player.exe file is written to %TEMP%, and a set170.exe file (the Karagany malware) is created in the %APPDATA% directory. When set170.exe is executed, Karagany checks if it is installed in its target location. If not, it installs itself to that location.
- 07:38:51-07:38:52 — The executed Karagany malware creates relevant directories and copies set170.exe as SearchIndexer.exe to the hard-coded %APPDATA%\Local\SearchIndexer\ installation directory.
- 07:38:53 — The malware establishes persistence by creating a link to SearchIndexer.exe in the user's Startup folder.
- 07:38:53-07:39:06 — Karagany writes several additional files and directories to disk, which matches the postinstall behavior described in Secureworks' detailed Karagany analysis.
At 05:58:31 the following morning (March 22), approximately 9:00 am Moscow Standard Time, the first evidence of interactive use of the malware appears in the forensic timeline (see Figure 2). The svchost filenames align with other Karagany samples observed by Secureworks analysts.
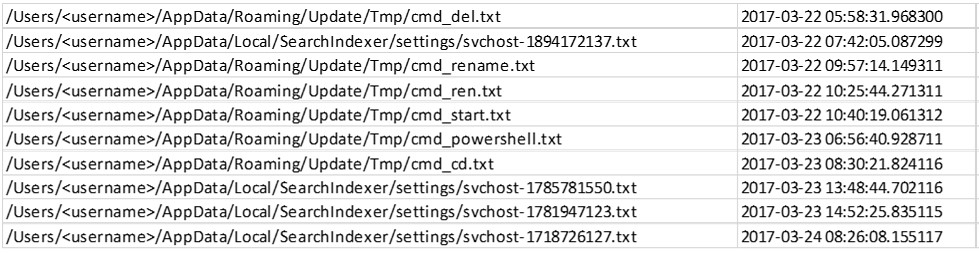
Figure 2. FN Info Creation dates for Karagany activity. (Source: Secureworks)
Additional analysis of the MFT showed the 'Std Info Creation date' for SearchIndexer.exe was June 1, 2013 (see Figure 3). All of the other timestamps associated with this file align with the 2017 timeline. The Std Info Creation date timestamp is rounded to the nearest hundreth of a second; it is the only timestamp from the compromised hard drive that contains four zeros. This type of rounding can indicate manually altered timestamps (also known as timestomping).
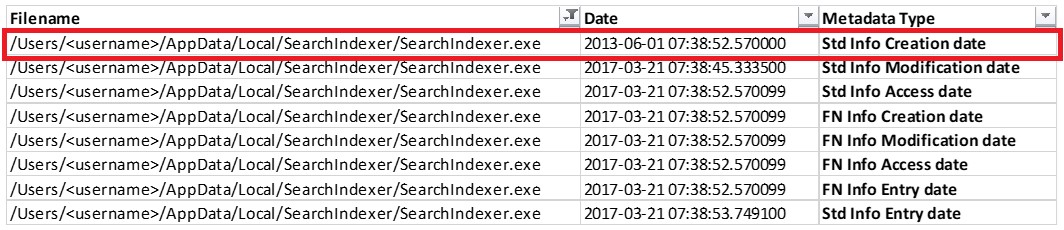
Figure 3. Timestamps associated with SearchIndexer.exe. (Source: Secureworks)
The forensic data shows that both the initial and final install_flash_player.exe files were modified at the same time the Karagany malware was installed (see Figure 4).
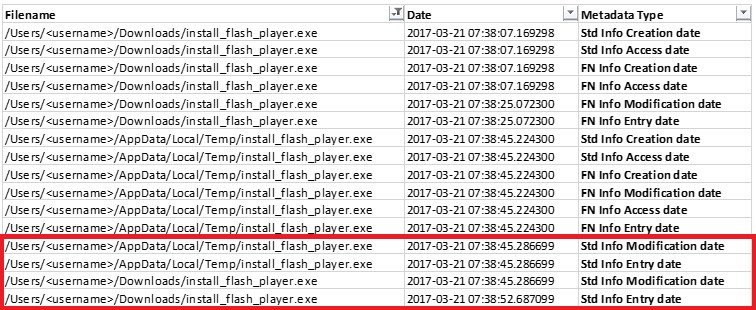
Figure 4. Timestamps for the initial and final install_flash_player.exe files. (Source: Secureworks)
As shown in Figure 5, the file size of the final Adobe Flash binary is smaller than the initial download. This discrepancy, in addition the lack of other events at the time of the Karagany download, indicate that the initial Adobe Flash binary download was the source of the Karagany malware. The byte sizes of set170.exe and the final Adobe binary do not equal the size of the initial install_flash_player.exe download. The remaining 86kB were likely associated with a wrapper to facilitate the installation. Secureworks analysts assess that once the malware was installed, the initial install_flash_player.exe download self-modified to remove all traces of the malicious content to leave only a legitimate Adobe Flash installer (version 25.0.0.127) binary on disk.
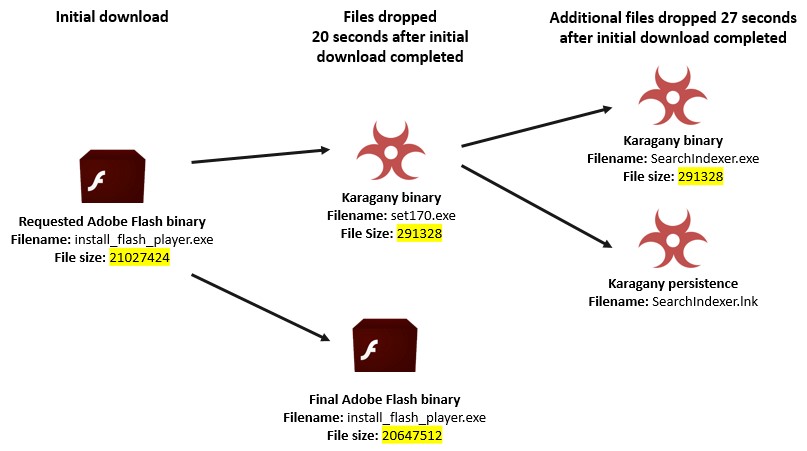
Figure 5. Discrepancy between the requested and delivered Flash installers. (Source: Secureworks)
How did this happen?
There are several credible explanations for how the Karagany payload was delivered alongside the Adobe installer file:
-
Option 1: Compromise of Adobe's website
Secureworks assessment: unlikely. Neither the investigation of the incident nor visibility across nearly 4,000 global organizations' networks revealed indications that Adobe's website was compromised during the attack timeframe. -
Option 2: Man-in-the-middle (MitM) attack using the victim's internal or gateway systems
Secureworks assessment: unlikely. Although it is possible that the threat actor could have used existing access to other systems in the victim's network to intercept and manipulate the response traffic, there was no evidence of this behavior in the environment. In addition, the nature and function of the infected host would have made it an unlikely target for a threat actor that had a presence in the network. -
Option 3: BGP hijack
Secureworks assessment: unlikely. Border Gateway Protocol (BGP) hijacking involves an unauthorized change in the routing of Internet traffic that sends an unsuspecting user's traffic through an attacker-controlled path that could be monitored and manipulated. After the request for the Adobe installer left the network, it could have been routed to attacker-controlled systems. However, these types of attacks can be “noisy” and are often detected by the security community. There was no evidence of this technique. -
Option 4: Man-on-the-side attack outside of the victim's network
Secureworks assessment: likely. Analysis of the environment suggests that the most likely scenario was that the threat actor used man-on-the-side techniques to intercept the Adobe installer request when it transited a compromised router outside of the victim organization and then return the trojanized response (see Figure 6).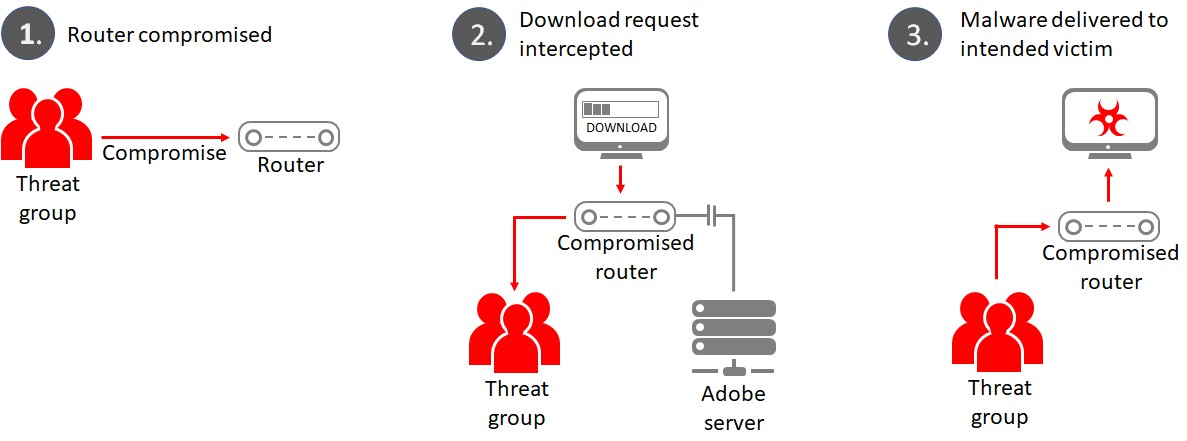
Figure 6. Suspected chain of events for man-on-the-side attack. (Source: Secureworks)
Russian government-sponsored threat actors have been linked to widespread router compromise campaigns in the past. The U.S. and UK governments published a joint advisory about some of these campaigns in 2018, after the UK government previously alerted users to edge router compromises in 2017. The example from the Secureworks engagement appears to demonstrate how targeted threat groups such as IRON LIBERTY can weaponize their access to routers and Internet infrastructure to gain initial access to targeted systems.
Conclusion
Using access to compromised routers to deliver malware is part of a growing trend of threat actors exploiting organizations' supply chains. Historically, threat actors gained access to targeted networks by using stolen credentials, abusing of trust relationships, or using access to software developer networks to trojanize software updates. Various incidents in 2018 affecting major service, software, and infrastructure providers highlight risks to organizations from outside their network perimeter.
The use of man-on-the-side techniques further complicates the challenge of defending against supply chain risks. As reports of targeted threat actors leveraging compromised routers become more common, it is important for organizations to consider their resilience to these techniques.
To provide additional insights about IRON LIBERTY and its malware, Secureworks Counter Threat Unit™ (CTU) researchers are publishing an analysis of the threat group and details about the Karagany malware and the MCMD remote access trojan (RAT). Additional findings and recommendations from Secureworks incident response engagements are highlighted in the Secureworks Incident Response Insights Report 2019.
[i] The original Karagany malware was an e-crime tool, but the IRON LIBERTY threat actors adopted and evolved the malware for their own use.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.