Recently, one of my favorite YouTube channels, Dave Jones' EEVblog, came under attack after having published a series of videos debunking a product claiming to vastly extend the life of alkaline batteries.
But just how do you "attack" a YouTube channel?
One does not simply DDoS Google in order to silence a YouTube channel; no one has that kind of bandwidth. Instead, what the attacker did was to spam the channel with "dislikes," a way to try and impact the revenue stream of the channel operator by manipulating YouTube's view recommendation system.
By checking his channel statistics, Dave noticed (like other channel owners who had criticized the same product) that the overwhelming majority of dislikes were coming from Vietnam, all at once in massive spikes that did not correlate with an increase in the number of views to the videos being disliked. Anyone (hopefully YouTube's abuse team) can see that the data points to large-scale vote manipulation. So why Vietnam? Dave speculated that it might be because Vietnam is a low-wage economy, where it is possible for residents to make an actual living doing menial tasks on the Internet for a meager income, making things like vote spamming a profitable business in those areas of the world. This is certainly a possibility, and we've seen reports of such operations in existence for many years in other countries.
However, there's another possibility – someone is using Vietnamese IP addresses as a proxy to hide their nefarious activity coming from a single machine, preloaded with thousands of either fake or stolen YouTube accounts. This would certainly be even more economical than paying workers to click "dislike" buttons, as it could be operated by a single individual with the help of some specialized software, and could be done more quickly (which could manifest itself as the huge temporal "dislike" spikes Dave's channel statistics showed). Now, most operations of this sort would simply use a botnet or a network of existing open proxy servers around the world. But there is something peculiar about Vietnam when it comes to Internet infrastructure that may lend itself to this theory.
In Vietnam, the Internet is provided by only five ISPs, even though it ranks 16th in the world in the number of Internet users, with tens of millions of subscribers. This means there are potentially millions of users all with the same broadband router model. If a vulnerability in the broadband router is found, it can be widely exploited, as happened last year with the Vietnamese ISP FPT. They provide a fiber-optic broadband router (model number EP9108W-4PE) to their subscribers in certain provinces. This model was reportedly hacked en masse and customers of the ISP had their routers hijacked/credentials changed, locking them out.
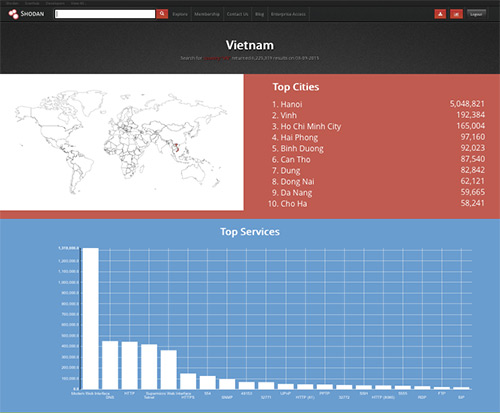
Using the Shodan search engine to examine Vietnamese IP space we see over a million modem web interfaces open to the world. All it takes to bounce traffic through a vulnerable broadband modem is to know the standard administrative username/password pair used by the ISP, something trivially obtained by analysis of the device's firmware image or even by brute force scanners. Once you can configure the modem, you can set up port forwarding and relay traffic inbound to a specific TCP port to an outside site (i.e. YouTube). This isn't a proxy in the conventional sense, where one can arbitrarily tunnel all HTTP traffic through another IP, but it can work in essentially the same way for a single destination site.
Vietnam is certainly not the only country with this problem. A rush to create broadband infrastructure in some countries where ISP choices are limited has led to a dangerous monoculture of vulnerable router deployments. As consumer operating systems are increasingly becoming more secure against exploitation that would cause them to become part of the botnet ecosystem, we are increasingly seeing broadband routers being abused for these purposes instead.
Vendors must do all they can to lock down the public interfaces of their broadband routers and audit the code to prevent exploitation from compromised devices behind the router as well. Recently in the U.S., the FCC is considering new rules that require Wi-Fi-enabled router devices to be secured against "unauthorized" updates, in order to prevent rogue users from modifying radio-frequency transmission power levels. While on the surface this sounds like a good thing, one side-effect it will have is to lock in yet another monoculture of router software, which may reduce the security of the Internet in return for allegedly reduced local radio-frequency interference (in the rare circumstance where someone actually bothers to change the transmission power setting on their custom firmware).
These new FCC rules also have a chilling effect on the work of the very viewers of Dave Jones' YouTube channel – electronic engineers who create new and innovate devices for the Field of Gadgets (FoG, formerly known as the Internet of Things/IoT). These new rules are unneeded and potentially harmful to the Internet. Instead of locking in vendor software to the devices (and locking out competition), our regulatory agencies should instead be demanding that vendors who sell routers to ISPs must secure their operating systems against exploitation and abuse. This is the major problem the world faces from these devices and is too often ignored by regulatory agencies. All of us in the security industry should take some time out of our workday today and give the FCC a little bit of negative feedback of our own.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

