Using Red Cloak, SecureWorks® Counter Threat Unit™ (CTU) researchers can observe an adversary issuing commands for lateral movement on a source system, and can view the resulting commands being run on the destination or target system.
CTU™ researchers have observed threat actors moving laterally between two systems (a source and a destination system) within a compromised infrastructure, often using tools native to the Microsoft Windows operating system. This is significant, as the adversary does not have to bring the tools and risk being detected through a mechanism such as antivirus software. Further, the native tools used by the adversary are typically command line tools, many of which leave very few artifacts.
Scheduled Tasks
After acquiring administrator credentials, an adversary can move between systems using Scheduled Tasks, functionality that is native to Windows systems. One approach is to create “unnamed” Scheduled Tasks. Figure 1 illustrates an adversary’s use of the at.exe tool to create a Scheduled Task on a remote system.
![]()
Figure 1. Scheduled Task created via at.exe. (Source: SecureWorks)
The command, in this case a batch file, is set to run at 01:19. In order for the batch file to be executed, it must first be copied to the destination system. This is easily accomplished by mapping a drive via the “net use” command, and then copying the file to desired location on the target system. Adversaries may create similar Scheduled Tasks by launching an executable file with various command line options rather than using a batch file.
Figure 2 illustrates what CTU researchers are able to observe when a Scheduled Task is executed on the destination system.

Figure 2. Scheduled Task running on target system. (Source: SecureWorks)
The Scheduled Task shown in Figure 2 runs the gsecdump credential theft tool (renamed to update.exe) and redirects the output to the file “hs.txt”. This task was created on the source system of the lateral movement using a command similar to the one shown in Figure 1.
PsExec
PsExec is a legitimate Windows tool provided through the Microsoft Sysinternals website. The powerful tool allows administrators to run applications on remote systems. However, it can also be used to open a reverse shell on a remote system (see Figure 3), allowing the adversary to enter commands that will be run with System-level privileges; that is, with a privilege level higher than administrator. This allows the adversary to run all the commands that an administrator can access (add or delete users, modify system settings, etc.).
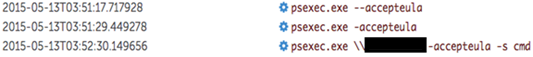
Figure 3. PsExec used to create a reverse shell. (Source: SecureWorks)
Expandito
CTU researchers observed a novel means of lateral movement that uses a tool they have named “Expandito.” In short, adversaries with remote desktop access to a system via Terminal Services can take advantage of the shared clipboard by encoding a binary file as text, and then producing a batch file that they copy, paste, and run on the destination system. This method of lateral movement relies on the use of a Visual Basic (VB) script that utilizes Windows Management Instrumentation (WMI), both of which are native to modern versions of the Microsoft Windows operating system.
The adversary runs the VB script, which compresses a binary executable file into a cabinet archive file format, and then Base64-encodes the resulting archive. The output of the VB script is a batch file containing the compressed and encoded executable file, along with wrapper code that will decode, decompress, and execute the binary file. The adversary then opens the batch file in a text editor such as Notepad, copies the batch file to their clipboard, and then pastes the contents into a file on the target system via the shared clipboard. Once the file has been copied, the adversary can simply double-click the file on the target system to execute their binary executable file.
Via Red Cloak, CTU researchers have observed the use of Expandito. When an adversary uses Expandito, the two processes illustrated in Figure 4 will appear sequentially.

Figure 4. Expandito processes with arguments. (Source: SecureWorks)
Other examples of lateral movement observed by CTU researchers are described in the SecureWorks blog posts Living off the Land and Sleeper Agents.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

