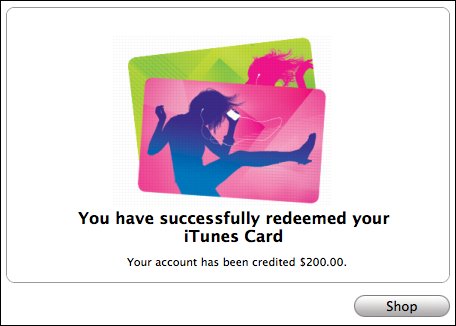
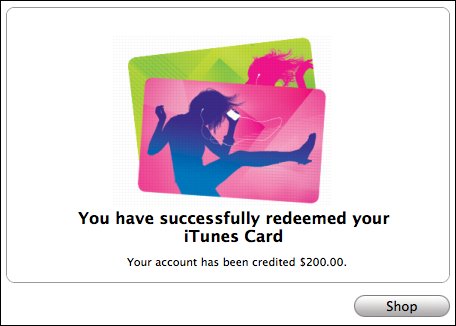
Earlier this week, reports began to circulate in the media about Chinese hackers selling $200 USD iTunes gift cards online for 17.90 RMB (about $2.60 USD). It was explained that these hackers were able to achieve the remarkable feat of cracking Apple's algorithm for generating the gift voucher codes, and were thus able to generate as many cards as they liked, all of which would be redeemable in the iTunes store.
This would be a pretty clever hack if it were true, however, something just isn't quite right here. Nowhere in these articles does it explain one simple thing - how do they manage to generate activated iTunes gift voucher codes? When you purchase an iTunes gift card, it has to be activated before it will work, otherwise you will get an inactive code message from the iTunes store when attempting to redeem it. If this were not the case, anyone could simply walk into any of the numerous retail outlets that stock iTunes cards, grab a hook-full and run out of the door with hundreds to thousands of dollars in iTunes money. This would be a shoplifter's dream! But, much to the dismay of those who have already tried this, the cards are simply worthless plastic until they are activated at the point-of-sale. Since this system works well and doesn't require a "secure" algorithm to generate the numbers, it stands to reason that the same system would be used for the online gift certificate vouchers.
But, third-party reports have confirmed that the voucher codes being sold by the Chinese hackers are in fact redeemable in iTunes (not sure how they verified this without exposing themselves to criminal charges however). So what is actually happening here? I see two likely scenarios: either the Chinese hackers have managed to penetrate Apple's internal network and/or iTunes gift card database and are directly stealing activated numbers before they can be used, or they are simply using stolen credit card numbers to purchase the cards.
Chinese hackers are certainly no strangers to penetrating networks via targeted attacks (although a targeted attack against Apple would not fit their previous modus operandi of using 0-day Windows exploits). They are also quite adept at SQL injection attacks, so a database hack isn't an unreasonable suggestion either.
But Occam?s razor suggests that this is more likely to be a case of the hackers using stolen credit card numbers to purchase the gift voucher codes from iTunes and then reselling them. Finding a way to "cash out" stolen credit card numbers is always a primary problem for credit card thieves, also known as "carders". Sometimes carders buy goods online and resell them, but it requires a real-world "drop" where the delivery of the physical items can be made without leading the police to their door. But transferring iTunes codes can be done electronically and anonymously, and since it is something with almost world-wide demand, there is never going to be a shortage of persons willing to buy the discounted codes without asking questions. And they can explain away the mystery of where the codes come from by simply saying, "Oh, we hacked the algorithm. Yeah, that's the ticket."
Since Apple has yet to comment on this, we can only speculate about these matters until the Chinese government takes some sort of action and arrests are made. In the meantime, if you know anyone whose credit card number has been used to make an unauthorized purchase of a large dollar value of iTunes gift codes, make sure to tell them to report it to the Internet Crime Complaint Center (IC3) right after they notify their credit card company of the fraud.
This would be a pretty clever hack if it were true, however, something just isn't quite right here. Nowhere in these articles does it explain one simple thing - how do they manage to generate activated iTunes gift voucher codes? When you purchase an iTunes gift card, it has to be activated before it will work, otherwise you will get an inactive code message from the iTunes store when attempting to redeem it. If this were not the case, anyone could simply walk into any of the numerous retail outlets that stock iTunes cards, grab a hook-full and run out of the door with hundreds to thousands of dollars in iTunes money. This would be a shoplifter's dream! But, much to the dismay of those who have already tried this, the cards are simply worthless plastic until they are activated at the point-of-sale. Since this system works well and doesn't require a "secure" algorithm to generate the numbers, it stands to reason that the same system would be used for the online gift certificate vouchers.
But, third-party reports have confirmed that the voucher codes being sold by the Chinese hackers are in fact redeemable in iTunes (not sure how they verified this without exposing themselves to criminal charges however). So what is actually happening here? I see two likely scenarios: either the Chinese hackers have managed to penetrate Apple's internal network and/or iTunes gift card database and are directly stealing activated numbers before they can be used, or they are simply using stolen credit card numbers to purchase the cards.
Chinese hackers are certainly no strangers to penetrating networks via targeted attacks (although a targeted attack against Apple would not fit their previous modus operandi of using 0-day Windows exploits). They are also quite adept at SQL injection attacks, so a database hack isn't an unreasonable suggestion either.
But Occam?s razor suggests that this is more likely to be a case of the hackers using stolen credit card numbers to purchase the gift voucher codes from iTunes and then reselling them. Finding a way to "cash out" stolen credit card numbers is always a primary problem for credit card thieves, also known as "carders". Sometimes carders buy goods online and resell them, but it requires a real-world "drop" where the delivery of the physical items can be made without leading the police to their door. But transferring iTunes codes can be done electronically and anonymously, and since it is something with almost world-wide demand, there is never going to be a shortage of persons willing to buy the discounted codes without asking questions. And they can explain away the mystery of where the codes come from by simply saying, "Oh, we hacked the algorithm. Yeah, that's the ticket."
Since Apple has yet to comment on this, we can only speculate about these matters until the Chinese government takes some sort of action and arrests are made. In the meantime, if you know anyone whose credit card number has been used to make an unauthorized purchase of a large dollar value of iTunes gift codes, make sure to tell them to report it to the Internet Crime Complaint Center (IC3) right after they notify their credit card company of the fraud.
Secureworks has been acquired by Sophos. To view all new blogs, including those on threat intelligence from the Counter Threat Unit, visit: https://news.sophos.com/en-us/.

